Media Summary: Start learning cybersecurity with CBT Nuggets. In this video, Keith Barker covers In this video, What is Threat Modeling? ( The video covers: W⦁ The video covers: ⦁
What Is Threat Modeling Threat Modeling Explained - Detailed Analysis & Overview
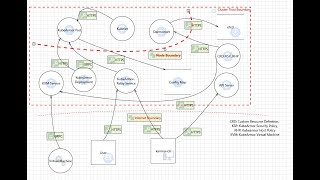
Start learning cybersecurity with CBT Nuggets. In this video, Keith Barker covers In this video, What is Threat Modeling? ( The video covers: W⦁ The video covers: ⦁ If I could save a company a million dollars on their security budget every year, this is how I'd do it! While most people don't think of ... MIT 6.858 Computer Systems Security, Fall 2014 View the complete course: Instructor: Nickolai ... In this video, we dive into the world of STRIDE
Hey everyone! I'm excited to be back! Today's video is on This is Part 3 of 5 of the "Application Security Considerations" video from the Study Notes and Theory Members Portal. To view the ... This video provide an introduction to the theory behind Master the essential difference between Trust Boundaries and Attack Surfaces in