Media Summary: In this video, we'll dive deeper into the first step of GOING FROM ZERO EXPERIENCE TO BECOMING A “CYBER SECURITY So we have some contextual information. You know the system criticality or if attackers are leveraging a certain
Vulnerability Management Training Part 2 Risk Assessment And Scanning - Detailed Analysis & Overview
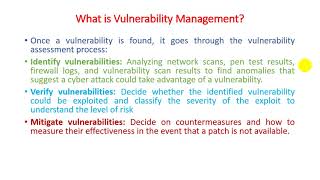
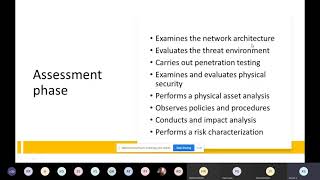
In this video, we'll dive deeper into the first step of GOING FROM ZERO EXPERIENCE TO BECOMING A “CYBER SECURITY So we have some contextual information. You know the system criticality or if attackers are leveraging a certain KirkpatrickPrice is on a mission to help 10000 people elevate the standards for cybersecurity and compliance. Join Our ... Move beyond static severity scores to quantifiable, contextual, and financially defensible 2 16 Cybersecurity Risk Assessment 4 New Zealand
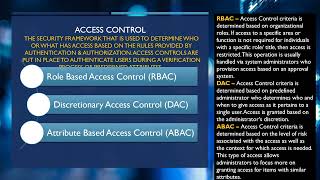
Looking to build strong cybersecurity and