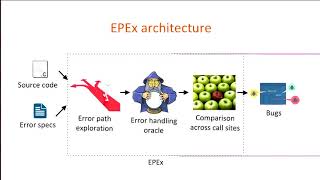
Media Summary: Inference of Error Specifications and Bug Detection Using Structural What IF Is Not Enough? Fixing Null Pointer Dereference A Linear Reconstruction Approach for Attribute
Usenix Security 24 Inference Of Error Specifications And Bug Detection Using Structural - Detailed Analysis & Overview
Inference of Error Specifications and Bug Detection Using Structural What IF Is Not Enough? Fixing Null Pointer Dereference A Linear Reconstruction Approach for Attribute Closed-Form Bounds for DP-SGD against Record-level SecurityNet: Assessing Machine Learning Vulnerabilities on Public Models Boyang Zhang, Zheng Li, Ziqing Yang, Xinlei He, ... AutoFHE: Automated Adaption of CNNs for Efficient Evaluation over FHE Wei Ao and Vishnu Naresh Boddeti, Michigan State ...
Voodoo: Memory Tagging, Authenticated Encryption, and "What do you want from theory alone?" Experimenting