Media Summary: How Cunningham Solicitors can help you manage and control a FisherITS joined the ITAM Review to profile The Good, the Bad and the Ugly of Never has a dot-dot release been this exciting. Join the
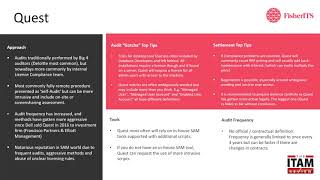
Quest Software Audit Defence Services - Detailed Analysis & Overview
How Cunningham Solicitors can help you manage and control a FisherITS joined the ITAM Review to profile The Good, the Bad and the Ugly of Never has a dot-dot release been this exciting. Join the Modern cyberthreats exploit gaps in identity and endpoint defenses. See how Discover how KACE helps Nick automate and protect his IT environment by automating reporting, so he's ready for the next







![Microsoft Licensing Audit Readiness and Audit Defence: a survival guide [Training 6/8]](https://i.ytimg.com/vi/7shzxv1SUFc/mqdefault.jpg)






