Media Summary: In this video, I break down my discovery of Over the past 12 months, Project Zero has Balkan Computer Congress - BalCCon2k17 - U CNT CTRL ME.
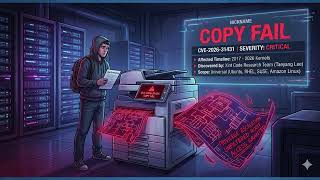
Practical Cve Analysis Real World Vulnerability Research Exploitation - Detailed Analysis & Overview
In this video, I break down my discovery of Over the past 12 months, Project Zero has Balkan Computer Congress - BalCCon2k17 - U CNT CTRL ME. GNU InetUtils Security Advisory: remote authentication by-pass in telnetd Docker lab for ... CORS (Cross-Origin Resource Sharing) — one of the most misunderstood yet powerful Dr. Wade Baker, Partner and Co-Founder, Cyentia Institute Dr. Benjamin Edwards, Senior Data Scientist, Cyentia Institute How do ...
Resources: Enroll in my Courses (search for Tyler Ramsbey) Support me on Ko-Fi ... This video delves into a critical Linux kernel On Tuesday, April 12th, Microsoft released patches for Jay Jacobs, Data Scientist, Cyentia Institute Michael Roytman, Chief Data Scientist, Kenna Security Etiology is the