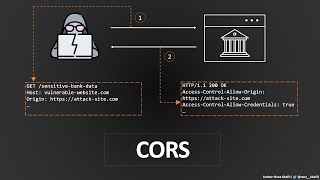
Media Summary: Ready to master AI security? Spots fill fast—save your seat now! ☕️ Enjoying the content? Support ... This video is just for educational purpose In this educational video, we'll be exploring the world of Cross-Origin Resource Sharing ... Uncover the Intricacies of Cross-Origin Resource Sharing (
Cors Misconfiguration Explained How Hackers Steal Data Via Cors 550 Bug Bounty - Detailed Analysis & Overview
Ready to master AI security? Spots fill fast—save your seat now! ☕️ Enjoying the content? Support ... This video is just for educational purpose In this educational video, we'll be exploring the world of Cross-Origin Resource Sharing ... Uncover the Intricacies of Cross-Origin Resource Sharing ( In this video, we explore a common security In this video, we cover the theory behind Cross-Origin Resource Sharing ( In this video, I'll walk you through how to chain reflected XSS
IF you Enjoyed the video, don't forget to Like , Subscribe, and turn on the Notification Bell to stay updated! WHO AM I ? I'm ...