Media Summary: In this cybersecurity training video (Part 6), we explore how persistence mechanisms work in Join us in the Black Hills InfoSec Discord server here: to keep the security conversation going! Learn attack ... In this exciting Python project tutorial, we dive into creating a TCP-based
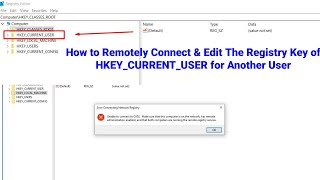
Backdoor Added To The Run Windows Registry Key - Detailed Analysis & Overview
In this cybersecurity training video (Part 6), we explore how persistence mechanisms work in Join us in the Black Hills InfoSec Discord server here: to keep the security conversation going! Learn attack ... In this exciting Python project tutorial, we dive into creating a TCP-based In this video I will explain you how to hack window through In this video we look at maintaining access to a In this cybersecurity training video, we explore how keylogging concepts work within system access scenarios and how security ...
Have you ever thought about it? ▽ Time Stamps: ▽ 0:00 - Intro & Root I enjoyed messing around with stuff, so I figured I would upload it because it's interesting. Just a quick camstudio upload to point out an interesting volatile (only available during user session) Want to break into IT with ZERO experience? Stop wasting time on random tutorials. Learn
















![[TutoriaL] Run Your Trojan Using Registry Key ...](https://i.ytimg.com/vi/1eVRwBvy-u0/mqdefault.jpg)
