Media Summary: So Devolder abilities was to two types of honor abilities that 92 Buget IoT Devices and Their Vulnerabilities - Video Presentation Lookout Co-Founder and Executive Chairman John Hering talks about how
A Talk On Iot Devices Their Vulnerabilities And Potential Exploits Beverley - Detailed Analysis & Overview
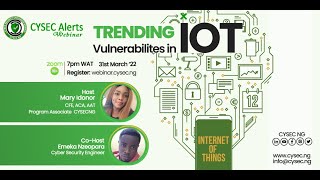
So Devolder abilities was to two types of honor abilities that 92 Buget IoT Devices and Their Vulnerabilities - Video Presentation Lookout Co-Founder and Executive Chairman John Hering talks about how In this insightful video, Bhanu Jagasia addresses the risks associated with 1. This YouTube channel focuses on exploring the security implications of Many people are now accepting intelligent
Cybersecurity is an important part of any business that cannot be ignored. If you are interested in obtaining high-quality protection ... Security Researchers over at Forescout have released a stunning report (dubbed Name Wreck) that details a slew of ... When the FBI warned that hackers can use the smart gadgets you have at home “to do a virtual drive-by of your digital life,” it was ... Timestamps 00:00:00 Intro 00:00:38 Understanding